News / Blog
The Rapid Advancement of AI-Driven Tools: Navigating Security Challenges and Protecting Your Business
Is AI Technology Right for Your Business? In 2025, artificial intelligence (AI) has become a cornerstone of business innovation, driving efficiency and opening new avenues for growth. However, as small to medium-sized business owners increasingly integrate AI-driven tools into their operations, it’s crucial to recognize and address the accompanying security challenges. Neglecting proper safeguards can…
Read MoreUpgrade to Windows 11: The Clock is Ticking for Windows 10 PCs
In the fast-paced world of technology, staying current with operating system updates is crucial for maintaining security, performance, and access to new features. As of February 2025, Microsoft has been actively encouraging users to transition from Windows 10 to Windows 11, especially with the expanded rollout of Windows 11 version 24H2 to all eligible Windows…
Read MoreElevating Your IT Strategy: vCIO Services by Synivate
In today’s fast-paced digital landscape, businesses of all sizes must prioritize effective IT management to remain competitive and secure. Synivate offers industry-leading vCIO services to help organizations strategically align their IT operations with business goals. Backed by a Certified Information Systems Security Professional (CISSP) on staff, our virtual CIO services address advanced compliance requirements and…
Read MoreUnlocking the Benefits of a SOC2 Certificate: Innovative Technology Solutions for Cybersecurity Compliance
Why a SOC2 Certificate Matters In today’s business environment, demonstrating trust and reliability is more critical than ever. Clients are increasingly seeking assurance that their data is handled securely and responsibly. A SOC2 certificate, designed to validate an organization’s adherence to stringent security, availability, processing integrity, confidentiality, and privacy standards, has become a gold standard…
Read MoreShielding Your Finances: A Comprehensive Guide to Credit Protection After a Data Breach
In our increasingly digital world, data breaches have become a common topic in the news, often involving high-profile companies. Take the recent incident with a major financial institution, for example—the breach exposed sensitive information of millions, showcasing how quickly our data can be compromised. Understanding the importance of credit protection after such events is vital,…
Read MoreNavigating the Future: Embracing Zero Trust Security and Conditional Access Policies in Microsoft 365
In today’s increasingly digitized landscape, the need for robust cybersecurity 2025 measures has never been more paramount. Organizations are enveloped in an era where security risks loom larger than ever before, and the stakes are incredibly high—data loss can mean severe financial consequences, tarnished reputations, and erosion of customer trust. As a result, the approach…
Read MoreUnderstanding and Mitigating the Risks of Deepfake Interviews in Business
As artificial intelligence continues to evolve, the emergence of deepfake technology poses unprecedented challenges to businesses. One alarming trend is the use of deepfake interviews to infiltrate companies, steal sensitive information, and disrupt operations. This article delves into the phenomenon of deepfake interviews, explores their implications for businesses, and highlights how Synivate’s network security services,…
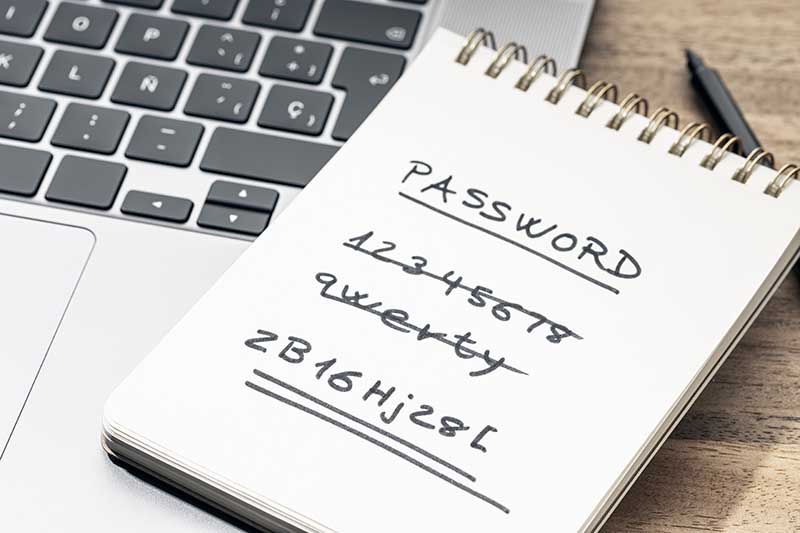
Read MoreManaging Mass Password Reset Issues: Key Strategies for IT Departments
In today’s fast-paced, digital-first business environment, ensuring the security and functionality of IT systems is a top priority. For companies navigating the complexities of technology, challenges like a mass password reset can significantly disrupt operations. When not managed effectively, these events strain IT resources, overwhelm help desks, and jeopardize business continuity. This article explores best…
Read MoreHow to Combat SaaS Data Breaches: Strengthening Security and Ensuring Business Continuity
The increasing frequency of SaaS data breaches has become a pressing issue for businesses worldwide. According to a report by AppOmni, 31% of organizations reported experiencing a SaaS data breach in 2024, a significant uptick from the previous year. These breaches pose serious risks, particularly as businesses underappreciate the complexity of their SaaS environments. In…
Read MoreHow to Bypass Security Protocols: Addressing Vulnerabilities in Industrial Remote-Access Gateways
Cybersecurity vulnerabilities in industrial and operational technology (OT) environments continue to pose significant risks, particularly when it comes to remote-access gateways. At DEF CON 32, researcher Moritz Abrell demonstrated how he was able to exploit serious flaws in the Ewon Cosy+, an industrial remote-access gateway, to bypass security protocols. This revelation serves as a reminder…
Read More